In an increasingly digitized world, ensuring the integrity and authenticity of documents has become a critical concern. The advent of advanced technologies has led to a surge in digital transactions, remote collaborations, and electronic document exchanges. However, this convenience also brings forth new challenges, such as the need to prevent unauthorized tampering, forgery, and data breaches. One potent solution that has emerged to address these concerns is the use of a digital signature generator, a tool that employs elevated encryption techniques to safeguard document authenticity. A digital signature generator operates on the principle of encryption, a process that converts data into a coded format, rendering it unreadable to unauthorized parties. Unlike a simple electronic signature, which is a graphical representation of a handwritten signature, a digital signature adds an extra layer of security by using cryptographic algorithms. These algorithms create a unique digital fingerprint of the document, often referred to as a hash value. This hash value is then encrypted using the sender’s private key, creating the digital signature.
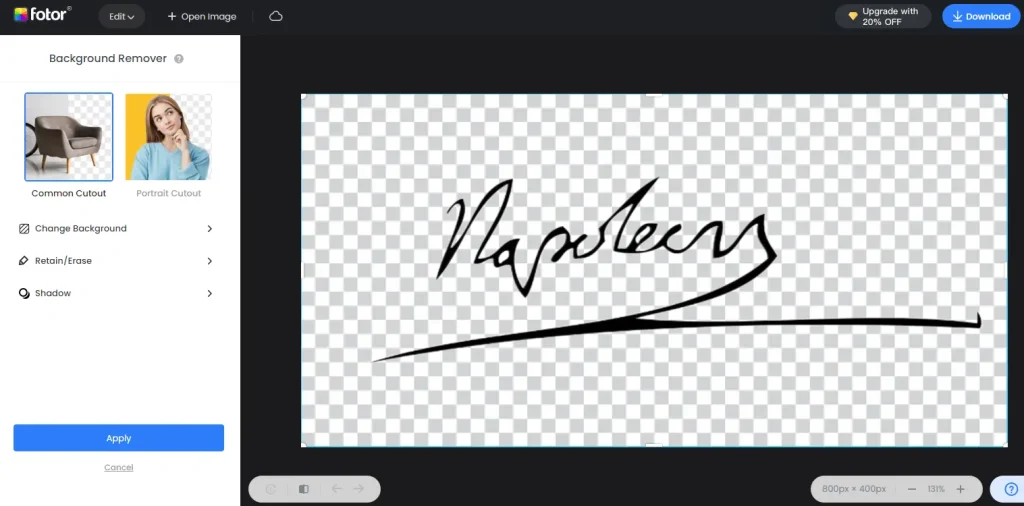
This signature is attached to the document and can be decrypted only with the sender’s public key, ensuring the authenticity and integrity of the document. One of the key advantages of e sign Generator is its ability to provide non-repudiation, meaning that the sender cannot deny having sent the document. Since the digital signature is uniquely linked to the sender’s private key, it becomes a reliable proof of origin. This becomes particularly crucial in legal and business contexts where the authenticity of a document can have significant consequences. Furthermore, digital signatures offer a level of security that surpasses traditional pen-and-paper signatures. The encrypted nature of digital signatures makes them extremely difficult to forge or alter without detection. Any modification to the document after the signature is applied will result in a mismatch between the original hash value and the recalculated hash value of the altered document, immediately alerting recipients to potential tampering. The use of a digital signature generator is not confined to large corporations or governmental bodies it has relevance for individuals as well. With the rise of remote work and online transactions, individuals are frequently required to sign contracts, agreements, or other sensitive documents.
Using a digital signature generator ensures that even personal documents remain secure and unaltered during transmission. The security of the private key is paramount, as its compromise would render the entire system vulnerable. Robust authentication and access controls must be implemented to prevent unauthorized access to the keys. Moreover, standards and protocols for digital signatures, such as those outlined in the standard, should be followed to ensure interoperability and security across different systems. The rise of digital transactions and remote collaborations has intensified the need for reliable document authentication methods. The digital signature generator, with its elevated encryption techniques and cryptographic algorithms, emerges as a powerful tool for safeguarding document authenticity. It not only prevents unauthorized tampering and forgery but also provides non-repudiation and enhances security in various contexts, from business transactions to personal document exchanges. As technology continues to evolve, integrating digital signature generators into everyday workflows can significantly contribute to a more secure and trustworthy digital environment.